 Unicorn Workflow
Unicorn Workflow
Abstract
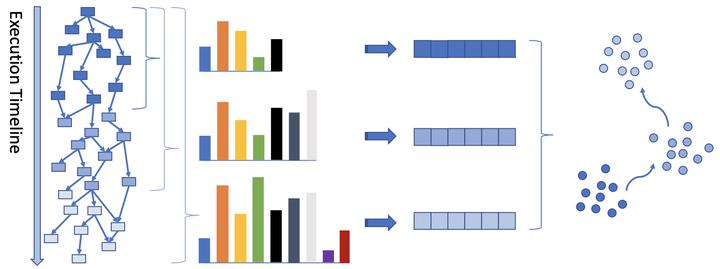
Advanced Persistent Threats (APTs) are difficult to detect due to their “low-and-slow” attack patterns and frequent use of zero-day exploits. We present Unicorn, an anomaly-based APT detector that effectively leverages data provenance analysis. From modeling to detection, Unicorn tailors its design specifically for the unique characteristics of APTs. Through extensive yet time-efficient graph analysis, Unicorn explores provenance graphs that provide rich contextual and historical information to identify stealthy anomalous activities without pre-defined attack signatures. Using a graph sketching technique, it summarizes long-running system execution with space efficiency to combat slow-acting attacks that take place over a long time span. Unicorn further improves its detection capability using a novel modeling approach to understand long-term behavior as the system evolves. Our evaluation shows that Unicorn outperforms an existing state-of-the-art APT detection system and detects real-life APT scenarios with high accuracy.